TRUSTED VENDORS – ESCROW SUPPORTED
Escrow Only • PGP Chat • Verified
Stay Ghost – Feds Watching
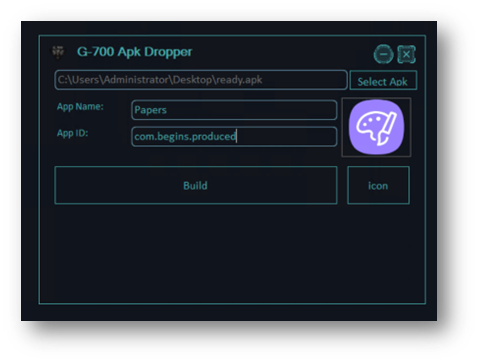
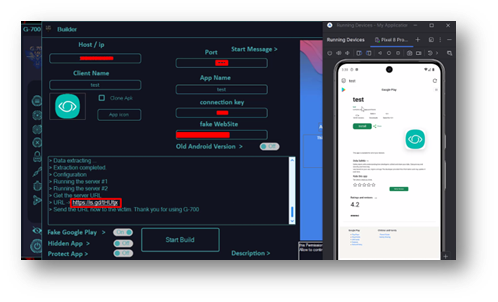
APK Dropper(Android Application Package) v3.0
APK Dropper(Android Application Package) v3.0
Introduction to APK Dropper v3.0 Malware
Android devices rely on APK (Android Application Package) files to install applications. While most APK files are legitimate, cybercriminals sometimes misuse this format to distribute malicious software.Softwa
One of the most common attack techniques is known as a dropper attack. A dropper is a program designed to install or “drop” additional malicious payloads onto a device after the initial application is installed.
Download Link
Instead of performing the harmful activity immediately, droppers first bypass detection mechanisms and later deploy the real malware.Antivirus & Malware
Key Characteristics of APK Dropper v3.0
Often disguised as legitimate apps
Installs hidden malware components
Attempts to bypass mobile security systems
Frequently used in multi-stage attacks
These techniques allow attackers to distribute malware more effectively.
Download Link
[/CENTER]
TRUSTED VENDORS – ESCROW SUPPORTED
Escrow Only • PGP Chat • Verified
Stay Ghost – Feds Watching